Many industrial organizations invest in bespoke anomaly management systems, believing a custom-built platform is the perfect fit. However, these systems often hide significant costs that erode their value, becoming an unexpected drain on resources and productivity. If your organization relies on a custom-built system, it’s time to examine its true cost.
Here are some hidden expenses and inefficiencies your bespoke anomaly management system might be silently accumulating:
1. The Ever-Escalating Cost of Maintenance and Support
Owning a bespoke system means bearing the full responsibility for ongoing maintenance, bug fixes, and security updates. Unlike off-the-shelf solutions that spread these costs, your organization carries the entire burden, often leading to:
- Dedicated IT Resources: You’ll likely need specialized internal staff or external consultants to understand and maintain your unique system architecture, incurring direct, recurring costs.
- Constant Patching: As operational needs evolve, your bespoke system requires significant, custom-coded modifications. This leads to a perpetual cycle of time-consuming and expensive development and patching.
- Growing Technical Debt: Over time, complex custom code can become difficult to manage, creating “technical debt” that slows future development and increases error likelihood.
2. Slow Feature Development and Missed Opportunities
The pace of technological innovation is rapid, and anomaly management best practices constantly evolve. A bespoke system inherently struggles to keep pace:
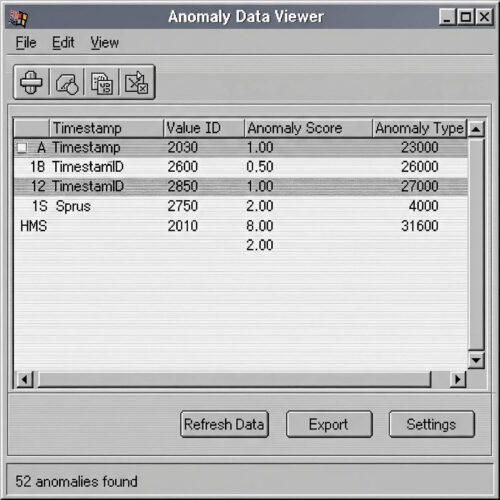
- Lagging Innovation: Developing new features in a custom system is slow and resource-intensive. This means missing out on the latest advancements in data analysis, predictive maintenance, and reporting readily available in modern, purpose-built platforms.
- Limited Agility: Adapting a bespoke system to new regulatory requirements or operational needs can take months or years, risking non-compliance or competitive disadvantage.
- Scalability Challenges: As operations grow, your bespoke system may struggle to scale efficiently, leading to performance issues and costly overhauls.
3. The Productivity Drain of Disconnected Workflows
A significant hidden cost of bespoke systems is their tendency to operate in isolation. If your anomaly management system isn’t seamlessly integrated with other operational workflows, you’re paying a hefty price in lost time and efficiency:
- Manual Data Transfer: Information often requires manual copying or re-entry into other systems like CMMS, ERP, or EAM, leading to errors and significant time waste.
- Fragmented View: Without integrated workflows, achieving a comprehensive understanding of asset health, maintenance history, and operational performance is difficult, hindering data-driven decision-making.
- Delayed Action: The time spent transferring information between disparate systems can significantly delay critical maintenance tasks, increasing downtime and potential safety risks.
- Fragile Integrations: Even custom connections are often fragile. Every IT stack update (e.g., database versions, security protocols) can break these integrations, requiring costly and time-consuming updates and retesting, diverting valuable IT resources.
4. Stop the Data Entry Madness: Embracing Direct Field Input
Many bespoke systems rely on outdated data input methods. Importing findings via spreadsheets is a prime example of a costly, error-prone process that should be eliminated:
- Eliminate Spreadsheet Chaos: Manually entering field inspection findings into spreadsheets, then importing them, leads to errors, inconsistencies, and significant time waste.
- Avoid Lost Context and Delays: The gap between field data collection and office data entry results in lost context, forgotten details, and delays in processing critical information.
- Enable Direct Field Data Capture: Inspectors and technicians can enter anomaly findings directly into a connected system from mobile devices in the field. This eliminates redundant data entry, improves accuracy, and accelerates the entire anomaly management process.
The HUVR Advantage: A Connected, Future-Ready Solution
At HUVR, we understand the complexities and hidden costs of traditional asset integrity approaches. Our unified asset integrity management platform overcomes bespoke system limitations by offering:
- Lower Total Cost of Ownership: We manage maintenance, security, and updates, freeing your internal resources and reducing operational expenses.
- Rapid Innovation: We continuously develop and deploy new features, ensuring you always access the latest advancements in anomaly management and data analytics.
- Seamless Workflow Integration: Our platform is built for connectivity, integrating with your existing CMMS, ERP, and other critical business systems for a holistic view of asset health.
- Direct Field Data Capture: Your teams can capture anomaly data directly from the field using mobile devices, eliminating manual data entry, improving accuracy, and accelerating response times.
- Extensive Configurability: HUVR offers broad configuration options to tailor the platform to your specific workflows, data fields, and reporting needs without custom code. This minimizes costly bespoke development and allows rapid adaptation.
- Robust API for Customization and Integration: For unique operational requirements or deeper system integrations, HUVR provides a comprehensive API. This enables your developers to build custom functionalities and connect with specialized third-party tools, all while leveraging the core platform’s stability and continuous updates.
Don’t let your bespoke anomaly management system silently drain your budget and hinder operational efficiency. Evaluate its true cost and consider a modern, integrated solution that supports your teams, optimizes workflows, and truly protects your critical assets.